This file type includes high resolution graphics and schematics when applicable.
Researchers from Kaspersky Labs, at their annual Security Analyst Summit (SAS), presented detailed findings of pervasive malware and embedded surveillance tools that have largely gone undetected for over a decade. The report implies that the surveillance tools were developed and deployed by the U.S. National Security Agency (NSA).
Some of the more startling revelations were:
• A program to systematically penetrate and map air-gapped systems.
• Malware operating at the firmware level that enabled discovery of encryption keys, cracking encryption algorithms and remaining in place through an operating system reinstall.
• Malware that replaced hard-drive firmware to create a secret storage area on a hard disk that would survive drive reformatting.
• Some of this malware has existed since around 2001, and has gone undetected until now.
These findings raise some interesting, and troubling questions for the cybersecurity industry, and specifically for those of us working within critical infrastructure. Chief among them: What are we doing to protect our systems?
Cyberwarfare: A Harsh Reality
Even if we accept the implication that the malware discovered by Kaspersky Labs was created by the NSA, it doesn’t imply that the critical infrastructure systems within the U.S. and our ally nations are safe from attack. There’s little doubt that China, Russia, and Iran have large, dedicated, and active cyberwarfare groups. If the U.S. has developed sophisticated cyberwarfare technology, it’s nearly certain that other countries either already have, or soon will, develop comparable technology.
Much of the technology described in the report from Kaspersky Labs is more than a decade old. Even if other countries are a decade behind the U.S., which is unlikely, then they would now have equivalent technology to infiltrate air-gapped systems, discover encryption keys, and remain undetected by standard security technologies.
Anyone building industrial control systems, vehicles, medical devices, or other critical infrastructure devices needs to take a new look at security. Air-gaps are a myth. The Kaspersky report detailed methods to compromise them, and many customers fail to maintain a strict air-gap. Hardware-enabled secure boot is a requirement. Security by obscurity must be abandoned as the relic that it is. The investment must be to build security into the foundations of every device being utilized within critical infrastructure.
Cybersecurity Investment—A Neglected Requirement
In February, President Barack Obama held a cybersecurity summit in Silicon Valley to push for greater awareness and investment in cybersecurity. At this conference, venture capitalist Venky Ganesan, the managing director of Menlo Ventures, a big investor in cybersecurity, warned that not enough was being done to protect systems from hackers, despite recent high-profile attacks.
“We still are not spending the right amount of time and resources and money on the cybersecurity problem. It's much bigger than people think,” said Ganesan. In fact, Ganesan remarked that only 5% of corporate information technology budgets are spent on security. “That’s the equivalent of protecting a Tiffany’s with a deadbolt,” he said. “We need to make sure that we spend the right amount of money because this is an existential threat to our society."
All too often, companies are looking at cybersecurity and asking: “What is the ROI for investing in security?” That is simply the wrong question to ask. Given the threat, cybersecurity should be considered a critical requirement, as is the case with safety. Key infrastructure, manufacturing, automotive, and other industries have invested billions into safety. Yet, despite the growing risk, government initiatives, and a growing awareness, companies are still, by and large, failing to invest in cybersecurity.
Security Challenges for Critical Infrastructure Devices
The Internet of Things (IoT) and Industrial IoT (IIoT) consist of a wildly diverse range of device types—from small to large, from simple to complex, and from consumer gadgets to sophisticated systems found in U.S. Department of Defense, utility, and industrial/manufacturing systems.
Embedded devices that are now part of the expanding Web-connected network differ greatly from standard PCs or other consumer devices. These industrial operational assets are commonly fixed function devices that have been designed specifically to perform a specialized task. Many use a specialized operating system such as VxWorks, Nucleus, INTEGRITY, or MQX, or a stripped-down version of Linux. Installing new software on the system in the field either requires a specialized upgrade process or is simply not supported. In most cases, these devices are optimized to minimize processing cycles and memory usage, and they don’t have extra processing resources available to support traditional security mechanisms.
As a result, standard PC security solutions won’t solve the challenges of embedded devices. In fact, given the specialized nature of embedded systems, PC security solutions won’t even run on most embedded devices.
Using multiple layers of protection is the driving principle for enterprise security. It includes firewalls, authentication/encryption, security protocols, and intrusion-detection/intrusion-prevention systems. These are well established and proven security principles. Despite this, firewalls are virtually absent in embedded systems, instead relying on simple password authentication and security protocols. This is based on assumptions that embedded devices are not attractive targets to hackers, embedded devices are not vulnerable to attacks, or that authentication and encryption can provide adequate protection for embedded devices. Such assumptions are no longer valid—the number and sophistication of attacks against embedded devices continues to rise, which demands greater security measures.
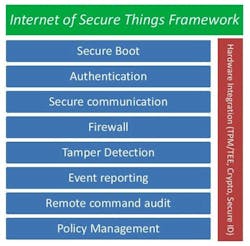
For over 25 years, cybersecurity has been a critical focus for large enterprises, whereas it has only recently become a focus for most engineers building embedded computing devices. “Experience is the best teacher, but the tuition is high”, or so goes the saying. Rather than learn all lessons through experience, embedded engineers can take a page from the enterprise security playbook. To ensure a device is secure, the following capabilities should be included (Fig. 1):
• Harden the device (secure boot, authentication, anti-tamper)
• Secure communication (security protocols, embedded firewall)
• Enable device visibility (remote command audit, event reporting)
• Enable security management (remote policy management, integration with security management systems).
These capabilities provide the foundation for building secure embedded devices.
Building Security into the Device
Building protection into the device itself provides a critical security layer—devices no longer depend on the corporate firewall as their sole layer of security. In addition, the security can be customized to the device’s needs.
A security solution for embedded devices must ensure that there’s been no tampering with the firmware. It must secure the data stored by the device, secure the communications in and out of the device, and protect the device from cyberattacks. This can only be achieved by including security in the early stages of design.
While there’s no one one-size-fits-all security solution for embedded devices, available solutions do provide a framework for OEMs. For example, Icon Labs’ Floodgate Security framework gives OEMs the core security capabilities required for securing their devices. This provides the flexibility needed to customize the solution to a device’s specific requirements, while ensuring that critical security capabilities are included (Fig. 2).
Summary
Kaspersky Labs’ report highlights the extent of today’s cyber threats. It is naïve to assume that the U.S. and its allies have a monopoly on such technology. Everyone involved in the development of technology for critical infrastructure needs to recognize the threats and begin investing in security solutions that provide the highest level of protection possible.
This file type includes high resolution graphics and schematics when applicable.
Today’s modern embedded devices and systems are complex, connected devices charged with performing critical functions. Including security in these devices is a critical design task. Security features must be considered early in the design process to ensure the device is protected from current advanced cyber-threats as well as likely more advanced attacks in the future. These steps are required to make your things secure and help create the Internet of Secure Things.