This file type includes high resolution graphics and schematics when applicable.
Is the Internet of Things (IoT) the same as Industrial IoT (IIoT)? Yes and no.
Yes, both are such broad terms—like the “cloud” and the “internet”—that they encompass almost any connected device, with IIoT leaning toward industrial applications. The challenge is that many applications destined to be categorized as IIoT will fall exclusively within the realm of industrial deployment, such as factory or warehouse automation. Meanwhile, applications like industrial lighting slip into the consumer or enterprise side, since at least the control applications run on user’s smartphones or tablets.
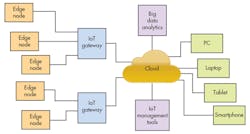
The basic IoT environment (Fig. 1) links devices (or edge nodes) to the cloud, often through gateways. These days, the cloud typically refers to computation and storage resources connected to the internet. IoT services like analytics and management tools utilize the data in the cloud. The raw and processed information is accessible via user interfaces from smartphones to PCs.
So What is IIoT?
Taking the most general view, IIoT is essentially machine-to-machine (M2M) support extended into the cloud. In this sense, IIoT is not really a new idea but, rather, new terminology describing existing systems. The big difference is how existing systems are changing and how available these technologies will be.
For example, large industrial organizations usually have networked control and management of their systems, and this is tied into a corporate server environment that will provide information that can be used to track the system. This can allow predictive analysis to anticipate failures so that maintenance can be done prior to a failure occurring. These systems may be built on lower level standards like Ethernet, TCP/IP, and SQL, but they were typically developed internally for a company.
The reason IoT and IIoT tend to overlap during any IoT discussion is that the tools and overall architecture tend to be the same. They use higher-level protocols on top of TCP/IP like MQTT and CoAP for data exchange.
The traditional cloud architecture (Fig. 2) simply uses embedded software on the Operations Technology (OT) platforms to push data to the cloud where Information Technology (IT) environments can both process it and provide it with users. This tends to be only a slight improvement over non-cloud environments.
Advanced IIoT environments (Fig. 3) move more system intelligence from the IT side to the OT side. This provides microcontrollers and embedded platforms with easy access to cloud environments, as well as access to data to authorized devices and users.
Chip Downing, senior director for Wind River's Aerospace and Defense division, notes that “Advanced sensor-to-cloud architectures enable systems intelligence along the entire path of business intelligence so decisions can be made autonomously on the OT side, on the side of running the day-to-day operations, enabling business intelligence in the IT side to focus more on business analysis, strategy, and the optimized flow of required assets and money.”
These more-advanced IIoT environments are targeting a range of application areas from smart factories to smart cities. The idea is to provide more information throughout the environment, and to allow more dynamic distribution of data and applications.
In general, IIoT tends to have a more structured connectivity environment because the system is more mission-critical than typical IoT applications. Response time tends to be an issue, whereas an IoT application like a fitness tracker can often store data until a wireless link is available. IIoT also tends to target existing equipment and standards, while consumer IoT devices are often new products.
IIoT Standards
IoT environments span a wider range of communication and services that previous models. This means there is a wider range of companies involved. It is also why IoT development and deployment tend to be more complicated and expensive although, in theory, the resulting system should be more efficient, more flexible and ultimately reduce costs while providing more functionality.
A number of visions and consortiums have arisen around IoT and IIoT. For example, Platform Industrie4.0, or Industry 4.0, is the vision behind the 4th Industrial Revolution that has been associated with the smart factory. The four primary characteristics of Industry 4.0 include vertical integration of smart systems, horizontal integration of global value chain networks, integrated product life cycle management, and incorporation of new and existing technologies.
Industry 4.0 has six design principles: interoperability, virtualization, decentralization, real time support, service orientation, and modularity.
A host of consortiums have arisen to address different IIoT aspects. For example, the Open Connectivity Foundation (OCF) incorporated the Open Interconnect Consortium (OIC) specifications, and the IoTivity open-source IoT framework. It highlights the difficulty of working with IIoT because of the range of alternatives available. For example, IoTivity is one of many IoT frameworks.
There are also other groups that address aspects of IoT and IIoT, such as the AllSeen Alliance and the Thread Group. These target specific aspects of IoT and IIoT, and their standards are often referenced by other organizations as part of a higher-level IoT/IIoT standard. The AllSeen Alliance provides services that enable connecting IoT devices together, while the Thread Group defines a wireless ecosystem for the OT device side of things.
The Industrial Internet Consortium (IIC) is part of the Object Management Group. IIC is focusing at IIoT, or Industrial Internet Systems (IIS) in IIC terminology, at a systems level rather than specifics like OCF’s IoTivity. IIS is divided into five domains: control, operations, information, application, and business. IIS is discussed in IIC’s Industrial Internet Reference Architecture, which is more oriented towards system models that can utilize different underlying technologies like Thread or IoTivity.
The challenge with IIoT systems is that they require high-level specifications like IIC’s because IIoT systems tend to be large and complex, incorporating end-to-end process control and management. Specifications for each level of functionality or communication are also required, so isolating them to specific areas such as Thread and local wireless communication allows the standards to be manageable and understandable.
IIoT Safety and Security
One of the big challenges for IIoT is safety and security, since IIoT often links devices and services to the cloud that used to be much more isolated. In many cases there was an “air gap” between an unconnected device and a corporate network or the internet. Providing a network link allows for real-time communication and often brings data to the cloud that was not obtainable in the past.
Most IoT frameworks or protocols incorporate one or more aspects of security, such as encryption of communication links to authentication of data or commands. Some even include support for security policies and other security and safety management. The problem is that an IIoT environment may incorporate a range of frameworks and protocols that have differing security features and management methods, leading to complexity and possible configuration errors that would allow security breaches.
Features like secure boot, security operating systems, and secure communications are the basis for a secure IoT environment, but even with all these in place it is possible to have security problems that can crop up due to errors in applications, operating systems, or device drivers. This is why a layered security environment is important for IIoT applications and why security needs to be a consideration when designing and implementing the system. It cannot be just the utilization of underlying security features or adding features like encrypted communication after the fact.
IIoT is the trend, but it will be challenging to incorporate existing networked systems into an overarching IIoT environment. There is no one IIoT standard, and a single one is unlikely given the plethora of conflicting and existing products and services that vendors have already. Still, there will be a continued push to implement IIoT because of the availability of more information for big data analysis, as well as more real-time information that will allow more just-in-time (JIT) features—such as product and raw material delivery, preventative maintenance, and real-time information about the overall process in smart factory or smart city environments.
Looking for parts? Go to SourceESB.
This file type includes high resolution graphics and schematics when applicable.
About the Author
William G. Wong
Senior Content Director - Electronic Design and Microwaves & RF
I am Editor of Electronic Design focusing on embedded, software, and systems. As Senior Content Director, I also manage Microwaves & RF and I work with a great team of editors to provide engineers, programmers, developers and technical managers with interesting and useful articles and videos on a regular basis. Check out our free newsletters to see the latest content.
You can send press releases for new products for possible coverage on the website. I am also interested in receiving contributed articles for publishing on our website. Use our template and send to me along with a signed release form.
Check out my blog, AltEmbedded on Electronic Design, as well as his latest articles on this site that are listed below.
You can visit my social media via these links:
- AltEmbedded on Electronic Design
- Bill Wong on Facebook
- @AltEmbedded on Twitter
- Bill Wong on LinkedIn
I earned a Bachelor of Electrical Engineering at the Georgia Institute of Technology and a Masters in Computer Science from Rutgers University. I still do a bit of programming using everything from C and C++ to Rust and Ada/SPARK. I do a bit of PHP programming for Drupal websites. I have posted a few Drupal modules.
I still get a hand on software and electronic hardware. Some of this can be found on our Kit Close-Up video series. You can also see me on many of our TechXchange Talk videos. I am interested in a range of projects from robotics to artificial intelligence.
Voice Your Opinion!
To join the conversation, and become an exclusive member of Electronic Design, create an account today!

Leaders relevant to this article: