Safety and security are mantras for the Internet of Things (IoT) with over 60% of the respondents in the recent Electronic Design Embedded Revolution survey indicating that these were important to their design. But what does it mean and how do we get there?
At one end of the spectrum is the initial system design and at the other testing to make sure the application does not break and cannot be compromised. The problem with the latter is that, like bug fixing, testing costs rise exponentially the farther from the development process one goes and the number of potential items to test rises as well.
The development is an iterative process and bugs are introduced and fixed in this process. This includes ones associated with safety and security as well as functional bugs that affect the intended application use. This is where coding standards, static analysis, and dynamic analysis come into play because they lighten the developer’s burden to create bug-free code. Unfortunately, the current state of affairs is not good.
According to the Barr Group’s 2017 Embedded Systems Safety & Security Survey:
- 9% of IoT designers don’t keep their source code in a version control system
- 56% don’t perform regular source code reviews for bugs and security holes
- 60% don’t use a static analysis tool to check the source code
- 25% don’t have a bug database or other system to track known issues
- 37% don’t utilize a written coding standard, and others don’t enforce one consistently
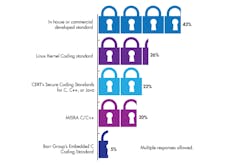
Likewise, our Embedded Revolution survey shows that only 43% have a coding standard. Coding standards are sometimes developed internally but many employ standard coding practices like MISRA C/C++.
Not all companies are employing coding standards in their development process (from Electronic Design’s 2017 Embedded Revolution survey).
The results are even worse for the use of static analysis tools. The problem is that automatic checking of coding standards and the use of static analysis tools can significantly reduce the number of undetected bugs that need to be fixed later in the design process. The costs in time and money to use these tools and procedures is not minor, but the payoff is significant simply because the cost of fixing bugs grows exponentially as the software moves from the developer to the field.
“Static analysis is a fundamental capability for identifying and eliminating potential coding flaws, weaknesses, and vulnerabilities,” says Jim McElroy, vice president of marketing for LDRA. “When used early and throughout the development process, static analysis can analyze and report on code clarity, maintainability, and testability, as well as help developers adhere to coding standards such as MISRA and CERT. This results in eliminating potential problems early where they are less costly to fix.”
The trends show more companies and developers employing coding standards and analysis tools but we are still well short of where we should be to provide products that will be safe and secure as the number of IoT devices moves into the billions.