By the time you arrived in the office this morning, you may have used radio-frequency identification (RFID) four times without being aware of it: when you inserted the key in your car, disabling the immobilizer circuit; when you drove through an unmanned toll booth, automatically paying your fee; when you used your cell phone to pay for your morning cappuccino; and when your ID badge registered your entry into the office. RFID may not be everywhere, but it is getting there.
The first passive transponders powered by incoming RF date back to the early 1970s, as does the vision for most of today’s manifold RFID applications. Yet only with advances in semiconductor technology, not to mention Moore’s Law, did RFID really start to take off.
For businesses, RFID offers an unprecedented opportunity for increasing productivity and improving customer experience by providing data at a very granular level and by automating services such as payments and record keeping. RFID is widely used in applications as varied as livestock identification, retail inventory management, medical records management, electronic toll collection, e-passports, and, more recently, mobile phones, which will be the key enabler of specific RFID technologies.
The market for RFID tags, the ID part of RFID, is growing rapidly and is expected to accelerate. IDTechEx, for example, forecasts that the number of passive RFID tags will rise from just under 3 billion units in 2011 to approximately 250 billion units in 2021.
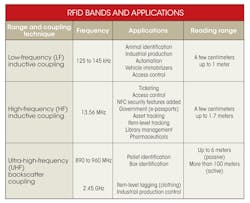
From an engineering perspective, RFID is not a single technology, and it varies with the frequency. Many carrier frequencies could be employed, but three predominate (see the table). LF uses the 125- to 135-KHz band. HF operates at 13.56 MHz. UHF primarily is used in the 865- to 955-MHz band, though it also may include the 2.4-GHz band.
Most RFID system design activity is focused on reader systems. The application and the characteristics of the transponders (tags) designed and manufactured by semiconductor companies primarily determine reader design. Broadly speaking, two types of tags can be used to communicate with the reader: active tags, which have an embedded battery, and passive tags, which do not. Passive tags are much more common and will be the only type discussed in this article.
Coupling Techniques
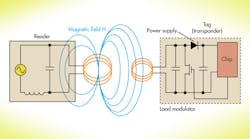
Electromagnetic coupling plays the dominant role in determining the reading range of passive tags. LF and HF RFID systems use inductive coupling. Energy is transferred from the coil of the reader to the coil of the transponder (tag) over a shared magnetic field.
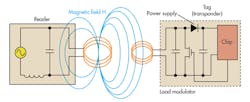
The reader antenna in LF and HF systems creates a strong magnetic field within an electromagnetic zone known as the near field, up to about one wavelength from the antenna. This magnetic field is strong enough to wake up the tag and supply it with the power needed to transmit its identification data to the reader. Inductive coupling also can be used to write to tags using the same energy-transfer mechanism (Fig. 1).
UHF RFID systems achieve a greater read range than LF and HF systems by operating in the “far field,” which extends from approximately two wavelengths from the antenna out to infinity. Using a technique known as backscatter coupling, the tag antenna receives the electromagnetic energy of the reader’s antenna, and the RFID chip uses that energy to change the load on the antenna and reflect back an altered signal that contains the identification information.
As a practical matter, tags are designed for specific applications and vary in frequency, memory size, the standard supported, and antenna design. Texas Instruments’ Tag-it HF-I Plus Transponder offers 2 kbits of memory in a miniature rectangle shape and is appropriate for product authentication, asset management, and supply-chain management. It is an HF tag that operates at 13.56 MHz.
At the opposite end of the memory scale, NXP’s HITag μ transponder integrates 128 kbits of memory. It is an LF tag suitable for livestock identification, laundry automation, and beer keg and gas cylinder logistics.
Design Goals
Specific RFID system reader characteristics are driven largely by the application, though several goals cross application boundaries. As in most engineering projects cost is important, which typically means minimizing the bill of materials and maximizing the added value provided by the tag manufacturer such as development tools, reference designs, and software.
Mechanical design should be robust and provide vandalism protection. Consideration should be given to governmental frequency allocations in the regions where the system will be deployed. It is also important for the system to be very easy to deploy and operate, because end users are not technicians.
Near Field Communication
Power consumption is also critical, particularly in battery-powered applications such as smart phones with embedded near field communication (NFC) functionality. Although it’s a subset of RFID technology, NFC has some distinctive enhancements:
• Shorter distance: NFC’s extremely short (<10 cm) operating range prevents accidental or unauthorized activation of the link. Encryption ensures even greater security.
• Intuitive linking procedure: NFC requires minimal effort by the end user. NFC-enabled smartphones, for example, initiate conversations with each other or with NFC readers simply by being held in close proximity or swiped.
• Ability to communicate with unpowered RFID products: NFC works in the conventional way between self-powered devices. It also supports communication with passive devices such as contactless smart cards or RF transponders.
• Synergy with Bluetooth and Wi-Fi: In addition to its complementary relationship with RFID technology, NFC has the built-in capability to communicate with devices that use Bluetooth and Wi-Fi wireless networks. As such, NFC provides a multi-protocol bridge between existing technologies.
According to IMS Research, NFC applications will grow rapidly, with mobile phones as the main driver. NFC-enabled mobile phones will jump by a factor of 10 between 2012 and 2017, reaching 1.2 billion units as manufacturers adopt wireless communications and payment technology in their products as a de facto standard. Shipments are projected to grow to 268 million units this year, which is up 123% from 120 million units in 2012. Major NFC applications include:
• Payments for entertainment tickets, taxi rides, or any point-of-sale (POS) application; store vouchers also can be stored on NFC phones
• Authentication and access control for secure buildings using an NFC smart phone; also PC login, locking/unlocking car doors, etc.
• Peer-to-peer data transfer between NFC-units such as smartphones, digital cameras, and tablet computers
• Communication links with Bluetooth or Wi-Fi for data transfer
• Providing access to digital information, as NFC devices will be able to read schedules from a smart poster to an NFC phone; downloading maps from a smart poster; and recording on your cell phone where you have parked your car.
NFC Technology Basics
NFC operates in the 13.56-MHz frequency range and has a data transmission rate from 106 to 424 kbits/s. To maximize its usefulness, the technology is backwards compatible with the Smart Card protocols based on ISO/IEC 14443 A and ISO/IEC 14443 B, as well as with the Sony FeliCa card (JIS X 6319-4).
For the exchange of information between two NFC devices, a new protocol was developed and defined in the ECMA-340 and ISO/IEC 18092 standards. The NFC Forum develops specifications that ensure the interoperability of NFC products.
NFC has three operating modes. In card emulation mode (passive mode), an NFC device behaves like an existing contactless card conforming to one of the legacy standards. In reader/writer mode (active mode), the NFC device is active and reads or writes to a passive legacy RFID tag. In peer-to-peer mode, two NFC devices exchange information. The initiator device (polling device) requires less power compared to the reader/writer mode because the target (listener) uses its own power supply.
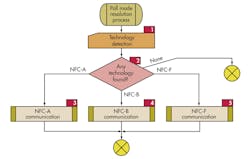
Each of the three legacy modes has its own transmission technology: NFC-A (backward compatible to ISO/IEC 14443 A); NFC-B (backward compatible to ISO/IEC 14443 B); and NFC-F (backward compatible to JIS X 6319-4). To support legacy technologies, an NFC device has to poll the listening device (tag) to determine which protocol to use: NFC-A, NFC-B, or NFC-F (Fig. 2).
Controller Chip
In NFC system design, the controller chip plays a central role. Deciding which communication mode to use is just the beginning. Among other typical MCU tasks, it has to monitor and control the transceiver, power management, and host computer interface. NFC-specific interfaces include the Secure Access Module (SAM) interface, the Subscriber Identity Module (SIM) interface, and the contactless technology (CLESS) interface.
NXP’s PN544 is a full-featured NFC controller with an embedded 80C51 core that is appropriate for integration into mobile phones. On the reader side, applications include mobile payment devices, transport and event ticketing, and object exchange (e.g., vCards and digital rights). Texas Instruments’ TRF7970ARHBT supports the same range of applications.
Conclusion
Although RFID applications typically are not high-performance, high-speed designs, there is a good deal of complexity at the system level due to different standards, frequency options, and, most important, application requirements. Every new design brings decisions about security, range, directionally of the signal, environmental conditions, power consumption, memory requirements, and interface design. Once the system architecture is carefully thought out, however, the numerous design tools and development kits provided primarily by semiconductor companies provide a clear path to a successful project.
Jack Shandle is a freelance writer specializing in a range of electronic technologies including wireless, the Smart Grid, and semiconductors. He has been chief editor of several electronics publications including Electronic Design and has written hundreds of articles.