Security and isolation go hand-in-hand these days. It’s rare to come across a design with only a single set of processing cores that aren’t supported by a separate security processor—one that often manages the more powerful computing system. For example, AMD’s latest embedded EPYC 3000 processor has a secure Cortex-A5 processor that provides a secure root-of-trust.
Isolating the security processor helps keeps it secure, thus helping it to improve overall system security. Likewise, many systems allow the security processor to control the isolation between other hardware and software aspects of the system. For example, a security processor may allow only certain hardware components to be accessible while the main processor operates in a particular mode. Oftentimes, a processor can access all peripherals in supervisor mode, but is much more limited when in user mode.
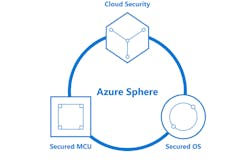
1. Azure Sphere includes a secure microcontroller platform architecture; a secure, Linux-based OS; and a cloud security component.
The new Azure Sphere environment is designed to deliver a secure Internet of Things (IoT) computing platform. Brought to you by Microsoft, MediaTek and Arm, it includes a secure microcontroller platform architecture; a Linux-based, secure operating system (OS) for the platform; and a cloud security component (Fig. 1). It’s designed to support the Arm Platform Security Architecture (PSA) and meet the Seven Properties of Highly Secure Devices. These include hardware root-of-trust, a small trusted computing base, defense in depth, compartmentalization, certificate-based authentication, renewable security, and failure reporting.
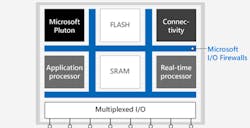
The platforms are based on Arm processor architectures. The first Azure Sphere-certified implementation is from MediaTek in the form of the MediaTek MT3620 (Fig. 2). The application processor is a 5000-MHz, 32-bit Arm Cortex-A7. It also has a pair of Cortex-M4F cores designed for real-time I/O support. These processors have security-controlled access to the peripherals that include ADC, GPIO, I2C, I2S, PWM, SPI, and UART ports.
2. The MediaTek MT3620 compartmentalizes the system using I/O firewalls between components.
The security processor is another Corex-M4F that’s part of the Pluton security system designed by Microsoft. On top of that, an Andes N9 32-bit RISC core handles the 1×1, dual-band, 802.11a/b/g/n Wi-Fi radio subsystem.
Isolating the communication system under control of the security processor allows secure updates to be managed independent of the applications and operating systems running on the application processors. It reduces the attack surface of the security system and simplifies the communication and software associated with the security support.
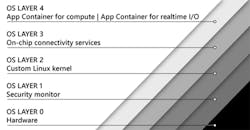
The Azure Sphere OS (Fig. 3) is actually spread across the hardware. It takes a container approach to applications running on the Cortex-A and Cortex-M platforms. This includes isolation configuration to allow access to a subset of resources based on the container’s need and security limitations.
3. The Azure Sphere OS layers are spread across the hardware, including app containers that run on the Cortex-A and Cortex-M4F cores.
Microsoft President Brad Smith said “After 43 years, this is the first day that we are announcing, and will be distributing, a custom Linux kernel.” Microsoft has supported embedded applications with its Windows operating system and the Windows IoT Core, but Azure Sphere OS provides support for a very small footprint system like MediaTek’s hardware.
The cloud-based Azure Sphere Security Service is designed to be a turnkey system that manages Azure Sphere devices. It offers brokering trust for device-to-device and device-to-cloud communication using the certificate-based authentication support in the hardware.
Small, multicore, secure SoCs with controlled access to peripherals and communication isn’t new. Many examples are out there, including Cypress Semiconductor’s PSoC 6 BLE Pioneer Kit with a Cortex-M4 and a Cortex-M0+ plus Bluetooth support. The trick is to provide the software support in a form that eases software development and integration.
Features like the Azure Sphere OS significantly reduce integration costs while minimizing security customization to higher-level configuration details. Likewise, it isolates the certificate-based management and authentication on-chip while integrating it the cloud-based Azure services.
Microsoft, MediaTek, and Arm are providing an impressive, integrated solution. A Wi-Fi-enabled IoT SoC addresses only a fraction of the IoT and Industrial IoT (IIoT) applications, but it’s a great start. It will support systems that allow third-party software to run in a secure, isolated environment in addition to providing a more secure environment overall.
About the Author
William G. Wong
Senior Content Director - Electronic Design and Microwaves & RF
I am Editor of Electronic Design focusing on embedded, software, and systems. As Senior Content Director, I also manage Microwaves & RF and I work with a great team of editors to provide engineers, programmers, developers and technical managers with interesting and useful articles and videos on a regular basis. Check out our free newsletters to see the latest content.
You can send press releases for new products for possible coverage on the website. I am also interested in receiving contributed articles for publishing on our website. Use our template and send to me along with a signed release form.
Check out my blog, AltEmbedded on Electronic Design, as well as his latest articles on this site that are listed below.
You can visit my social media via these links:
- AltEmbedded on Electronic Design
- Bill Wong on Facebook
- @AltEmbedded on Twitter
- Bill Wong on LinkedIn
I earned a Bachelor of Electrical Engineering at the Georgia Institute of Technology and a Masters in Computer Science from Rutgers University. I still do a bit of programming using everything from C and C++ to Rust and Ada/SPARK. I do a bit of PHP programming for Drupal websites. I have posted a few Drupal modules.
I still get a hand on software and electronic hardware. Some of this can be found on our Kit Close-Up video series. You can also see me on many of our TechXchange Talk videos. I am interested in a range of projects from robotics to artificial intelligence.