The fast pace of news and social media on the internet can be a good thing, but it also may cause significant problems of quickly spreading incorrect information. Recent examples include an apparent confrontation between native Americans and students in Washington, D.C., involving a video that was an abridged version of a longer one that showed a bit more of the surrounding crowd. The longer version showed a few other protesters that were verbally harassing the other two groups.
A similar incorrect analysis of a Wi-Fi chipset hack was also in the news. Denis Selianin is a researcher with Embedi who discovered a bug in the firmware for the Marvell Avastar 88W897 Wi-Fi chipset. The chipset is used in a number of popular devices like the Sony PlayStation4, Xbox One, and Microsoft Surface laptops, along with some smartphones and Chromebooks.
A number of exploits were discovered using fuzzing techniques to determine that malformed packets could be used to corrupt memory in a way to allow for execution of malicious code. The issue isn’t that the method of attack or its results were wrong, but rather the analysis that brought into question the underlying RTOS that turned out to be ThreadX from Express Logic.
I suspect quite a few of you are developing for ThreadX—it’s a very popular and well-tested RTOS. There are over six billion devices running it at this point, according to their website (Fig. 1). If the fault was due to the RTOS, then it could have a significant impact on lots of devices.
1. ThreadX has been used in more than six billion devices.
As it turns out, ThreadX isn’t at fault and the problems are application errors. This is similar to issues with other well-known operating systems like Microsoft Windows, when an application running on the operating system can be corrupted. The problems encountered with the chipset firmware were typical buffer overrun problems common with C applications, where oversight must be handled by the programmer. It’s the same type of error that caused the OpenSSL Heartbleed bug.
Cart Before the Horse
I had my doubts about ThreadX being the culprit when I read the ZDNet article “WiFi firmware bug affects laptops, smartphones, routers, gaming devices.” The article has since been modified to exonerate ThreadX, although the problem is still there and is still significant. How the firmware will be updated for the host of devices using the Marvell chipset is another story, and potentially one without a happy ending given how reluctant vendors are of fixing devices in the field. I reached out to Express Logic before finalizing my article.
Bill Lamie, Express Logic’s President and CEO, said “It’s very unfortunate that we weren’t aware of the Embedi report before it was published. If we had known about the research, we would have been able to correct some of the factual misrepresentations regarding ThreadX. The vulnerability cited by the author lies with the application firmware and drivers running on the Marvell Avastar 88W8897 SoC, and has absolutely nothing to do with the ThreadX RTOS itself. In fact, the problem as described could occur on any RTOS, OS, or even without an RTOS. None of the extensive 6.2 billion deployments using the ThreadX RTOS are in any way compromised by the ThreadX RTOS code or behavior. This is entirely an application firmware issue."
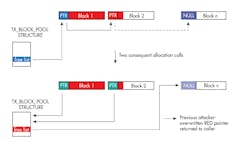
Part of the researcher’s challenge was that the analysis was done in conjunction with reverse engineering the software. That’s not easy by any means, but it does highlight how someone might misunderstand what part of the system was in error since the RTOS resources tend to be ubiquitous. The buffer overflow problem winds up corrupting the memory-block allocation chain (Fig. 2). Of course, it’s up to the driver software to limit memory use of a block. The attack would not occur on other platforms running ThreadX unless the associated driver firmware had similar problems. Then the exploit would likely be different.
2. The Marvell firmware breach is caused by a buffer overflow problem that corrupts the memory-block allocation chain. (Source: Embedi)
What this problem does highlight is the importance of a layered security and stability approach to a systems design. The chipset is similar to many, especially module-based solutions, that operate independently of the host. In this case, the exploit would compromise the chipset; however, attacking the host is another matter. The compromised chipset could be turned into a man-in-the-middle attack that examines and modifies the data stream. This can be mitigated, though, using encryption and authentication schemes that are managed by the host. Communication could still be disrupted, but further attacks on the host and its operation can be prevented.
However, the challenge for developers is significant, since the communication chipset/module is often used to manage communication security as well as managing transport. The host typically assumes that the data is secure.
Most developers know not to jump the gun when this type of problem arises. Judicious research and planned mitigation are more appropriate once the problem is correctly understood. So, ThreadX users need not panic, but Avastar 88W897 Wi-Fi chipset users need more research. The attacks may be applicable to all instances or only certain versions.
About the Author
William G. Wong
Senior Content Director - Electronic Design and Microwaves & RF
I am Editor of Electronic Design focusing on embedded, software, and systems. As Senior Content Director, I also manage Microwaves & RF and I work with a great team of editors to provide engineers, programmers, developers and technical managers with interesting and useful articles and videos on a regular basis. Check out our free newsletters to see the latest content.
You can send press releases for new products for possible coverage on the website. I am also interested in receiving contributed articles for publishing on our website. Use our template and send to me along with a signed release form.
Check out my blog, AltEmbedded on Electronic Design, as well as his latest articles on this site that are listed below.
You can visit my social media via these links:
- AltEmbedded on Electronic Design
- Bill Wong on Facebook
- @AltEmbedded on Twitter
- Bill Wong on LinkedIn
I earned a Bachelor of Electrical Engineering at the Georgia Institute of Technology and a Masters in Computer Science from Rutgers University. I still do a bit of programming using everything from C and C++ to Rust and Ada/SPARK. I do a bit of PHP programming for Drupal websites. I have posted a few Drupal modules.
I still get a hand on software and electronic hardware. Some of this can be found on our Kit Close-Up video series. You can also see me on many of our TechXchange Talk videos. I am interested in a range of projects from robotics to artificial intelligence.