A Cybersecurity Strategy to Secure the Real World
Download this article in PDF format.
The development of the smartphone started a trend of connected devices that not only perform some form of computing and decision-making, but it’s also changed how we relate with the world around us. These devices are connected through networks and cloud services that provide easy access and sharing of information.
To solve for market demand, a rapidly multiplying number of connected devices are designed to transform and innovate how we seamlessly interface with the world. This trend is changing how we relate to the automobile and factory—and it’s creating cybersecurity headaches for industry integrators. In these markets, there’s a much higher demand to operate reliably, which presents unique cybersecurity challenges when extending the connected edge.
For instance, the automobile is no longer simply a tool used to get us from point A to point B. It’s becoming a platform that provides us new means to interact with the world and improve our quality of life. This is being achieved through connectivity and the sharing of data, such as how to optimize battery performance or update navigation with changing landscapes. The automobile platform is becoming a way to connect and integrate services in a fashion that mimics the development of the smartphone in an environment that demands near-absolute safety, integrity, and accessibility.
The industrial market is undergoing significant changes as new technology advances serve as a catalyst for higher productivity. The demand for increased productivity is changing how we interoperate and interact with the factory. Thus, the need to interface with the factory in a more intuitive and seamless manner is driving the next industrial revolution.
The wave of advances defining Industry 4.0 has led to increased connectivity and requirements for access in the factory. The devices at the edge need to be more capable, moving the analytics further to the edge and boosting functionality, autonomy, and connectivity. The data links between the devices in the factory and the traditional field connection point need to adapt to be more capable; providing increased visibility and control from the cloud. In an industry known for focusing on stability and availability, demand for flexibility is now on the rise.
Solving for the need to interface with the world around us in a more seamless and intuitive manner drives new capabilities and technologies. However, a major byproduct of these developments is the need for security. Cybersecurity is a principal factor in market segments that demand high reliability and safety.
Those who have malicious intent, commonly called bad actors, can exist within or outside an organizational system and can have many different motivations. The threat to connected devices exists both through the network as well as physical access. Cybersecurity applied to these edge devices need to adequately address the threat.
On that front, cybersecurity is a key element of Analog Devices’ (ADI) strategy, not only because it’s necessary in our markets, but because it’s a catalyst for enabling our customers’ systems and increasing the value of information gleaned from our sensors.
Why Cybersecurity is Hard to Understand
Cybersecurity can be difficult to wrap your arms around because it’s a constantly changing, complex problem and a factor at every point in a system or device lifecycle. Security is a system solution, and the system is only as strong as its weakest link. A significant number of cyberattacks occur today, with successful attacks increasing as systems become more complex.
System vulnerabilities can be demonstrated though many examples of weak links. In 2016, automotive key fobs were compromised for an entire fleet because only four root keys were used for the past 20 years. In 2011, high-assurance identity tokens were exploited through exposure of manufacturing artifacts created and stored on the factory floor. In 2017, a vehicle was accessed through the cellular link, which gave hackers the ability to update the operating system and rewrite the program remotely. The Heartbleed Open SSL buffer over-read vulnerability left 200,000 active servers and devices vulnerable and without the means to receive security updates today.
To further elaborate on why cybersecurity can be hard to understand, it’s because security is never finalized. As new vulnerabilities are discovered and new methods of hacking devices are established, devices and systems must constantly be updated to adjust to security changes.
On top of that, the interplay of systems and devices presents a complex security problem that’s not solved by any one solution. The solution requires a secure system architecture with an in-depth defense approach. Past methods, such as air-gapped systems, don’t provide adequate protection in today’s connected world, with the availability of physical access to devices on the network. The problem needs to be addressed as early as possible in the design cycle to allow for a security-by-design approach, and an architecture and lifecycle design that accounts for ever-changing and growing threats.
Why Implement Cybersecurity at the Edge?
Cybersecurity has traditionally been perceived as an IT problem, requiring implementation of good network protocols, operating-system and application protocols, firewalls, malware protection, and other solutions designed to guard against network attacks. However, there isn’t always unilateral agreement on what constitutes the edge.
For network providers, the edge is often considered as the router, gateway, PC, tablet, or other high-functioning device. In the industrial automation space, it may be the actuator that controls a pump. In today’s changing environment, these edge devices are adapting to include more functionality and higher levels of connectivity. These changes alter the risk assessment of the system. Where cybersecurity might not have been needed previously, these devices may become the weakest link in a system if proper measures aren’t taken to guard against the risks.
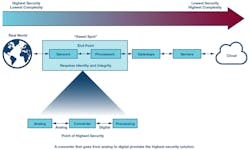
Implementing cybersecurity at the edge gives users more confidence in the data. To reach the highest levels of security, security must be applied much earlier in the signal chain. Providing confidence that the data hasn’t been manipulated by validating the source enables a higher level of confidence in the decisions being made from that data. ADI is in a unique position to redefine the secure edge by leveraging existing solutions that connect the physical world to the digital world.
When it comes to cybersecurity, complexity is the enemy. For every 1,000 lines of code, there are two to three coding errors, which provide avenues to maliciously exploit a system. Implementing cybersecurity at the point of lowest complexity creates an environment that’s more assured to have correctly implemented security. Secure operations can take place within security boundaries implemented within the edge devices, pushing the chain of trust closer to the real world.
In highly complex networks, organizations and individuals must continually update applications and configurations to protect against the latest threats. At the device level, one can limit the secure operations to a footprint that becomes much more manageable throughout the product’s lifecycle.
Implementing cybersecurity where the physical world meets the digital world offers the highest level of security by establishing trusted data earlier in the signal chain. As IT and OT converge, cybersecurity will not simply be an IT network problem. Devices that haven’t traditionally been security-hardened will need to provide a root of trust in the data, and security features will need to be applied based on the risk assessment and constraints of the system. Substantiating identity and integrity at the edge establishes trust in the data earlier, instilling more confidence that the data is accurate.
A Cybersecurity Strategy to Address the Market
Analog Devices, one of the leaders in precision sensing, has developed an array of devices that are relied on to make real-time decisions in high-reliability markets. Along with crafting advanced technologies that push current capabilities, the company is addressing problems created as byproducts of these advances. Cybersecurity is at the forefront of its priorities.
There are distinct differences in how these markets perceive cybersecurity and their level of maturity for adopting security solutions. ADI has a range of secure crypto solutions targeted for the defense and government market. The cybersecurity expertise was obtained through the acquisition of Sypris Electronics. By leveraging this strong base in nation-state-level cryptographic solutions, the company is pivoting into adjacent markets that must operate with high reliability. It’s pushing cybersecurity solutions further to the edge, and that includes precision sensing, which is an ADI stronghold.
Cybersecurity applies to all markets. The industrial sector has similarly seen numerous attacks that range in severity. Some of the most significant have been nation-state attacks on key infrastructure targets and targets that could result in loss of life. These attacks have been initiated through malware injected into systems, typically through physical access of a control unit or PLC connected to the factory network.
With the emergence of Industry 4.0, the point of attack will continue to expand closer to the edge as traditional I/O devices start having more control over operations and are connected through Ethernet to the PLC or directly to a cloud. With this ever-expanding functionality and higher functioning connectivity on a network, the once relatively safe edge devices become a much higher risk to the system.
Due to the sophistication of attacks in this market space, the ability to implement cybersecurity techniques correctly becomes paramount to the overall system vulnerability. This implementation requires an accurate threat assessment to understand potential points of attack and layering on security solutions to adequately protect against these threat vectors. For an at-the-edge device, establishing appropriate security boundaries and enabling a hardware root of trust greatly increases the system security posture.
For more on Analog Devices’ cybersecurity solutions, please visit the company’s website.
Erik Halthen, who specializes in cybersecurity solutions, is Market Development Manager at Analog Devices Inc. He can be reached at [email protected].
About the Author
Erik Halthen
Market Development Manager
Erik Halthen, part of Analog Devices’ acquisition of Sypris Electronics in 2016, brings extensive expertise in cybersecurity solutions. As part of ADI’s cybersecurity center of excellence, Erik has taken on the role of market development manager and leveraged his experience as a program manager to develop leading security solutions that meet key market demands in automotive, industrial, and IoT. Erik’s experience leading teams in the development and integration of new security technologies, combined with a strong background in business, partners with customers to revolutionize how IoT security is executed from the edge to the cloud.
Voice Your Opinion!
To join the conversation, and become an exclusive member of Electronic Design, create an account today!

Leaders relevant to this article: