Harden Process Control Systems to Meet Growing Threats
What you'll learn:
- The role and importance of segmentation, authentication, authorization, and privilege.
- The role and importance of secure firmware and configuration management.
- The role and importance of physical and electrical protection.
In 2023, a South Carolina poultry processing plant was hit by what authorities believe was an insider attack by a disgruntled former employee. The consequences were substantial with routine chemical treatments disrupted, risking quality control and basic food safety.
That incident, still being investigated, was apparently conducted as a “cyberattack” via networked computers and high-level programs. However, many processing facilities have vulnerabilities that extend to the device level, where an accident or a deliberate act of sabotage could cause subtle or very serious damage, in many cases with a low likelihood of detection.
Therefore, in an environment where disruptions and attacks of all kinds seem to be growing more likely, it’s prudent to look at ways to harden all aspects of process control so that they’re more resistant to attacks. Some potential steps to consider include segmentation; authentication, authorization and privilege; secure firmware and configuration management; and physical and electrical protection.
What’s the Role of Segmentation in Process Control Hardening?
Segmentation is a key strategy for limiting the impact of cyber-type attacks conducted by an insider or an outsider.
>>Download the PDF of this article, and check out the TechXchange for similarly themed articles and videos
First and foremost, strive to place each node (such as a PLC, PAC, RTU, or an intelligent sensor) on a separate VLAN or ring segment isolated from corporate IT traffic. Implementing firewalls or Layer-3 switches between process, supervisory, and enterprise layers is also helpful. As a default, deny inbound traffic.
Another powerful option is the adoption of data diodes. These network security devices enforce a one-way data flow between two networks, ensuring data can only travel out of a protected network, but never back in. To achieve that, a physical, often optical, connection is used to provide a security layer that’s impossible to bypass remotely because it’s based on physics, not software rules like a firewall. This kind of unidirectional gateway can still deliver telemetry to historians, or it can be utilized for analytics.
Protocol management is another straightforward means of reducing risk. Disable unused ports and services, such as FTP, Telnet, and legacy HTTP, should be disabled and enforce encrypted variants (e.g., OPC UA with TLS, Modbus TCP over VPN, and secure MQTT).
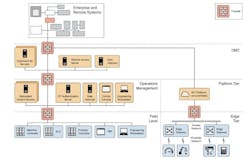
Distributed control aystems (DCS), which already offer considerable resilience, can also be made more specifically resistant to cyberattacks as outlined in the NIST publication “NIST SP 800-82r3 – Guide to Operational Technology (OT) Security” (see figure).
What Role Do Authentication, Authorization and Privilege Play in Hardening?
While authentication, authorization, and privilege represent to some extent a management and human factors topic, designers can require unique credentials per device and should try to prevent the adoption of shared “admin” or vendor defaults. A “best practice” is to implement role-based access control (RBAC); for example, differentiating between operators and engineers. Some other related best practices include:
• Storing credentials in hardened jump servers or management consoles, not in PLC logic.
• Employing multi-factor authentication on any human-machine interface (HMI) or remote access path.
• Regularly auditing all logins and configuration changes.
What’s the Role of Secure Firmware and Configuration Management in Hardening?
A comparatively simple practice, which may begin with design, is maintaining hash-verified firmware images from the original manufacturer. “Hash-verified” means verifying the integrity of firmware to ensure it hasn’t been altered. This is done by comparing its cryptographic hash to a trusted hash value. Hash verification ensures the firmware is both the authentic and untampered version intended by the developer.
While less susceptible to a design strategy, every effort should be made to restrict or disable in-situ firmware updates unless authenticated and logged.
Code-signing and trusted boot processes should be built-in if possible. In addition, it can be helpful to encourage the offline retention as read-only backups of configuration files and ladder logic. Also helpful are processes for configuration baselining that can provide an alert if unexpected parameter or logic changes occur.
How Can Physical and Electrical Protection Contribute to Hardening?
This is where good hardware design and cybersecurity align. Steps to take include:
- Shield and route signal cables to prevent injection or interference attacks.
- Ensure the safety of FPGAs.
- Potting of components and subsystems can reduce the potential for tampering.
- Install surge and EMI suppression so attackers can’t exploit induced transients. Induced transients can be used by attackers to introduce temporary, anomalous electrical or data signals to trigger vulnerabilities in physical systems and their control logic, effectively bypassing normal defenses and potentially allowing exploitation.
- Protect field devices with environmental sensors (door-open, vibration, temperature) to detect tampering.
- Finally, device-level hardening can further frustrate any attempt to compromise operations. This can include disabling or securing debug ports (JTAG, serial console), using secure bootloaders and read-only memory areas for critical firmware, implementing rate-limiting on communication interfaces to resist flooding or replay, and deploying anomaly detection at the node where you can monitor for command frequency or payload deviations.
References
“Security Hardening of Industrial Control Systems through Attribute Based Access Control,” Dec. 5, 2023. (https://www.acsac.org/2023/workshops/icss/shwetha-gowdanakatte-paper.pdf)
“Enhancing Cybersecurity Visibility in Industrial Control Systems (ICS)."
>>Download the PDF of this article, and check out the TechXchange for similarly themed articles and videos
About the Author

Alan Earls
Contributing Editor
Voice Your Opinion!
To join the conversation, and become an exclusive member of Electronic Design, create an account today!

Leaders relevant to this article: