Time to Think About the How and Where of Cryptography
This article is part of the Communication Series: The Cryptography Handbook
Members can download this article in PDF format.
Threats from various sources relentlessly attack all our connected systems. Connected systems don’t necessarily mean those connected to the internet. It could also include a pulse oximeter connected to a patient in a hospital environment or a printer cartridge connected to a printer. The current plethora of Internet of Things (IoT) devices like thermostats and refrigerators are also susceptible to hacking. Let’s look at a few of these threats and learn how to protect your devices and see what kind of planning you need to do.
Threats
Two kind of threats face developers today: threats to systems and threats to security ICs.
Threats to systems have been well covered by other sources, so we’ll focus on threats to security ICs. A security IC can be attacked by one or more of the following attack methods:
- Side-channel attacks: Examples include a glitch attack (active) and differential power analysis (passive).
- Invasive attacks: Decapping and micro-probing to find open ports and traces that can be exploited.
- Line snooping: One example is a man-in-the-middle attack.
- Memory array tampering: One example is a cold boot attack.
Most of the time, side-channel attacks are noninvasive attacks, i.e., they don’t destroy the IC. Decapping and micro-probing, which physically investigate various features of the IC, are invasive attacks that can destroy the IC.
We’re won’t go into too much detail about how these attacks are carried out, but we’ll present a couple of simple examples.
Active Side-Channel Attack: Glitch Attack
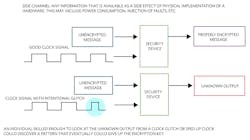
A side channel includes any information that’s available as a side effect of the physical implementation of hardware. This may include power consumption, injection of faults, etc. Figure 1 shows a type of side-channel attack using clock glitches. This is an example of a noninvasive attack.
An individual skilled enough to look at the unknown output from a clock glitch or sped-up clock could discover a pattern that could eventually reveal an encryption key.
Decapsulation
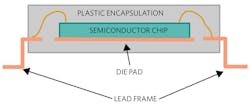
Decapsulation, also knows as de-capping, involves soaking the plastic package that encapsulates the silicon die into fuming nitric acid and melting the package away (Fig. 2). Normally, before that’s done, the lead frame holding the semiconductor die is secured on a frame. This is considered an invasive attack.
Semiconductor Package
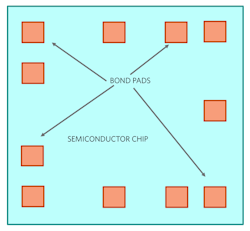
Once the package is melted away, the die gets exposed and this gives the hacker an opportunity to directly probe all of the available pads, including pads that the manufacturer used for internal setup (Fig. 3). They can also polish away the top protective glass and access the internal interconnects of the device. Using this direct method, the hacker will try to gain access to the device’s secrets.
Countermeasures
To prevent people with malicious intent from breaking into a secure device, it must be designed with features that not only provide security, but also protect the device from attacks.
For example, Maxim’s secure devices have robust countermeasures to protect against these attacks. Some of the implemented features include:
- Patented physically unclonable function (PUF) technology to secure device data.
- Actively monitored die shield that detects and reacts to intrusion attempts.
- All stored data are cryptographically protected from discovery.
Security Planning
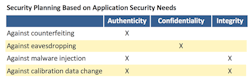
Depending on the application need, the user must decide what features of cryptography are appropriate for deployment. The table below gives some examples of application needs and the resultant measures that must be applied.
For example, if someone is trying to prevent a medical surgical tool from being counterfeited, they must ensure that every time a tool is connected to the host controller (Fig. 4), the tool’s authenticity is checked. It will also require protection against any malware from being installed in the tool, which could potentially harm the patient. The need to protect any calibration data that was stored is paramount as well.
However, because the possibility of snooping between the tool and the host controller is next to impossible due to closed system connectivity, this system will not require protection against eavesdropping. Thus, in this case, the system designer should plan for all of the protections under the “Authenticity” column, but can skip unnecessary protection listed under the “Confidentiality” column.
Conclusion
Threats to ICs are ever present and come from many sources. A system designer needs to be aware of the types of threats and plan accordingly. This article gave you some simple insights into how that can be achieved.
But if you’re a busy product developer with a tight deadline, do you really have the time to be an expert in this field as well as complete your design on time? Probably not. That’s where the use of a secure authenticator designed and built by industry experts may be a good option.
The next article in this series will review how secure authentication products can be quickly deployed for cryptographic security needs.
Read more from the Communication Series: The Cryptography Handbook
Zia A. Sardar is Principal Member of Technical Staff at Maxim Integrated.
About the Author

Zia Sardar
Applications Engineer, Maxim Integrated
Zia is an Applications Engineer at Maxim Integrated. Prior to joining Maxim, Zia worked at Advanced Micro Devices and ATI Technologies, focusing on graphics processors and PCIe bridge products. He holds an M.S. degree in computer engineering and a B.S. degree in electrical engineering from Northeastern University in Boston, Massachusetts.
Voice Your Opinion!
To join the conversation, and become an exclusive member of Electronic Design, create an account today!

Leaders relevant to this article: