Why LoRa Technology Should Be the DNA of IoT
This article appeared in Evaluation Engineering and has been published here with permission.
What you'll learn:
- What makes LoRa such a good fit for IoT connectivity?
- Breaking down how LoRa and LoRaWAN systems work.
- Specific applications particularly suited to LoRa.
As we enter the connected era, our reliance on the Internet of Things (IoT) will be more pronounced. The ability to actively transmit large volumes of data across myriads of physical devices, vehicles, and other items will be a game-changer for people and enterprises.
Machina Research estimates there will be 27 billion IoT connections in 2025 generating $3 trillion in revenue. While short-range wireless technologies will continue to account for about 72% of all IoT connections in 2025, Machina Research estimates that 11% of IoT connections will use low power, wide area network (LPWAN) technologies, showing a real market opportunity for solutions built around long range and low power features.
To support this trend, the IoT needs reliable technology that will enable full use of the various connective applications. Data transmission is reliant on secure networks with wide reach and low power consumption. LoRa devices and wireless radio frequency technology (LoRa technology), a long-range, low-power wireless radio frequency (RF) platform, is the solution. LoRa technology is versatile enough to function in both dense urban environments and dispersed rural areas, making it an ideal IoT solution for any number of use cases.
A LoRa-based IoT solution begins with a LoRa-enabled embedded sensor that sends data through an LPWAN gateway application (Fig. 1). It is then sent to a network server and routed to application servers and cloud IoT services. The applications interpret the data collected from the embedded sensors using techniques such as machine learning and artificial intelligence, providing valuable information to the end user securely.
Secure IoT
Gartner found that nearly 20 percent of organizations observed at least one IoT-based attack in the past three years. The firm also forecasts that worldwide spending on IoT security will reach $3.1 billion in 2021.
The LoRaWAN specification is a low-power, wide area networking protocol designed to wirelessly connect battery-operated ‘things’ to the internet in regional, national or global networks. A key element of the LoRaWAN network protocol is security. Its baseline authentication and security framework is based on the AES 128 encryption scheme as implemented by IEEE 802.15.4/2006 Annex B [IEEE802154], for example. By using separate keys for user data encryption and authentication/network integrity, LoRaWAN offers a higher level of security compared to single key implementations.
There are two methods for an IoT device or so-called end node to be connected to a LoRaWAN network. The first one is called Activation by Personalization (ABP). In this method, the Network Session Key and the Application Session Key are already stored in the IoT Device together with a unique 32-bit Device Address and a unique 24-bit Network ID that identifies the specific LoRaWAN Network the device is meant to connect to.
The default method of connecting a LoRaWAN\IoT Device is through a procedure called Over the Air Activation (OOTA). In this method, each IoT Device will send out a Join Request Message to the Network Server, which then forwards this message to a Join Server (Fig. 2).
This Join Request MAC command will contain three data fields (Fig. 3). An IEEE-defined 64-bit DevEUI (think of it as an “Ethernet MAC” address for LoRa Devices) uniquely identifies this specific LoRaWAN/end-node. It will also send a unique AppEUI identifying the Application Server this specific end-node wants to connect to. The final data is a random 2-byte Device Token. The Join Server will store these random Device Tokens from previous Join Requests Messages from each End Node.
If the Join Server receives a future Join Request from a specific end-node with a Device Token identical to a recently received one, the Join Server will ignore the Join Request. This will prevent so called “Replay Attacks” where a hacker could somehow capture a Join Request radio message from a particular end-node and replay (i.e. re-transmit) the same message with the intent to get the original end-device disconnected from the LoRaWAN Network.
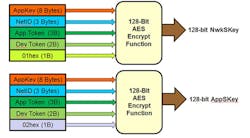
Only if the Join Server is able to authenticate the combination of DevEUI and AppEUI will it then issue a unique 32-bit Device Address, a unique 24bit Network ID and a 3-byte Application token. These parameters will be received by the end-node in a so-called Join Response command from the Network Server. The end-node can then generate its own security keys. Figure 3 shows what fields are used to generate both the Application Session Key (AppSKey) and the Network Session Key (NwkSKey). One of the key fields to generate these keys is the AppKey. This is a unique 128-bit fixed value that is unique for each end node.
Designed with security in mind, LoRa deployments are the lifeblood of IoT solutions. Now let’s take a look at some common examples of LoRa-based IoT applications.
Global Supply-Chain Tracking
Vehicle fleets—like trucks, cars, ships and planes and—are the backbone of many businesses with global markets. By utilizing IoT fleet tracking, businesses have the data necessary to make informed cost-saving decisions. Embedded sensors can assist with effective fuel management through route planning, geographic vehicle tracking and providing predictive maintenance updates for planned repairs and reduced downtime. An entire fleet can be equipped with embedded sensors in less than a day and maintained with minimal effort as its low power consumption allows sensor batteries to last up to 20 years.
Embedded sensors may also be used to monitor the goods these fleets ferry throughout a global supply chain. Shipping companies can monitor and automatically adjust environmental conditions in refrigerated units, reducing the risk of severe temperature fluctuations. A desired feature when shipping sensitive perishables such as food, across long distances. Additionally, sensors can periodically relay geographical data on shipment location, providing users the ability to monitor items and ensure it reaches its intended destination.
Smart Agriculture
Only 3% of the Earth’s water is accessible freshwater and 70 percent of that is consumed by the agriculture industry. IoT solutions are essential in providing farmers with the information they need to make decisions on how to efficiently use the resources at their disposal. Through a LoRa-based deployment using smart irrigation, farmers are able to reduce the risk of crops dying from over irrigation or drying out.
Irrigation zones are equipped with a remote sensor platform and soil moisture sensors at various depths. The sensor station’s LoRa transceiver periodically sends a message packet to a LoRa gateway containing data on soil moisture levels. The gateway can support up to 1,000 sensor deployments within a six-mile radius. The soil data is then analyzed by a dedicated or cloud-based server, where it can be then sent to the end user who can configure the application for manual or automatic irrigation in dry zones. By integrating sensors with irrigation systems, farmers are able to save up to 30 percent of their water usage while maintain optimal crop yields, making LoRa Technology an ideal IoT solution for the agricultural industry.
Smart Homes
As a home owner, there are many things to keep track of. Water usage, lights and temperature to name a few. In the connected era, IoT solutions can simplify the management of utilities, making them readily accessible no matter where the owner is within their network. LoRa-enabled smart home applications extend to thermostats, sprinklers, door, locks and energy outlets. Similar to smart refrigerators, LoRa-based thermostats are able to monitor household temperature and adjust as necessary throughout the day. Smart irrigation applications monitor when and how long sprinklers should be active. These applications are all readily accessible through a mobile device providing homeowners and property managers the ability to control multiple utilities and conserve energy.
Additionally, smart home IoT solutions can also aid in protecting homes and buildings from water damage. Mold is a problem plaguing many homeowners, but in order for it to grow, the ideal conditions must be present. Moisture and humidity are the key factors to mold growth and both can be monitored using a LoRa-based embedded sensor. Similar to other smart home utilities, de-humidifiers can be activated through a LoRa network. Additionally, low cost and low power sensors can be installed in water-prone areas such as under sinks, near pipes and windows. By identifying moisture and temperature levels throughout a house, homeowners are able to be immediately notified when a leak occurs and fix as necessary to prevent mold growth.
The Road Ahead
With the world embracing the connected era, more IoT applications are bound to be developed to meet new challenges. LoRa Technology will continue providing critical support to IoT solutions, empowering end users with long range, low power networks. As the DNA of IoT, LoRa Technology has a bright future, offering different industries the tools it needs to join the IoT movement.
About the Author
Marc Pégulu
Vice President, IoT Strategy and Products, Semtech
Marc Pégulu has been vice president of IoT in the wireless and sensing products group at Semtech since June 2015. He held the position of vice president of wireless and sensing products from June 2014. Prior to this appointment, he held the position of director of marketing and applications. Pégulu joined the Company in March 2006 and was involved in several key technology initiatives, including LoRa wireless and software-defined modem technologies. Prior to joining Semtech, he held positions in chips and systems development at Thomson CSF, Thales, Atmel, and DibCom in France and China.
Pégulu holds a Master of Science degree in electronics and telecommunications from Institut National Polytechnique of Grenoble, France, and is a graduate of the Executive MBA program of ESCP Europe.
Voice Your Opinion!
To join the conversation, and become an exclusive member of Electronic Design, create an account today!

Leaders relevant to this article: