TechXchange: Hypervisors, Containers, and Virtual Machines
Building embedded system software can be challenging given the wide range of constraints from the amount of available memory to hardware security capabilities. Technologies like hypervisors, containers, and virtual machines (VMs) can make this task easier by providing isolation between software components. The content in this TechXchange focuses on the different approaches to application and operating-system isolation and security.
Click to see the list of topics
- Virtualization Versus Containers
- Hypervisor and Virtual Machine Architectures
- Languages and Virtual Machines
- Containers, Interpreters and Kernel Architectures
- Virtualization, Containers and Security
- Virtual Machine and Container Environments
- I/O Virtualization
We're interested in what environment you're targeting now with respect to virtualization and containers. Take our quick poll and see what others are using.
Virtualization vs. Containers
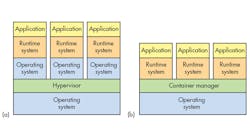
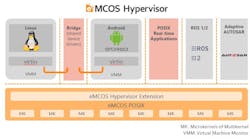
There are many ways to provide isolated software environments depending on the hardware available plus the security and performance requirements of the application. Hardware virtualization tends to be the most secure, but it requires additional hardware found in higher-end processors that's often missing in microcontrollers.
Articles in this section look at the different approaches, including hardware virtualization, containers with and without operating-system support, and embedded language environments like Java and Python that utilize software VMs.
Languages and Virtual Machines
While it's possible to build VMs for programming languages like C and C++, the results aren't necessarily useful or as secure as one might like simply due to the limited boundaries of the languages.
On the other hand, some high-level languages like Python and Java can be used with interpreted software- or compiler-based VMs that limit the access of applications within the confines of the language specification. These articles and videos examine what's available and the ensuing tradeoffs.
Containers, Interpreters, and Kernel Architectures
Containers provide software isolation within an operating system or operating environment. This can be done using compiler technology to make sure the application can't exceed the limits of the virtual machine. These articles look at the different implementations and approaches available to embedded developers.
Virtualization, Containers, and Security
One reason for using virtualization or containers is to improve security. Isolating applications can help reduce platform-level threats, but developers need to understand the details as well as the types of attacks that can be perpetrated. These articles examine aspects of system security, isolation guarantees, and attack surfaces, as well as common misconceptions about security.
I/O Virtualization
I/O virtualization is typically associated with hardware virtualization. It can isolate the application from the underlying hardware as well as enable sharing of a single device among different VMs in a transparent fashion. For example, a single Ethernet adapter can connect all of the VMs on a machine to the network.
Different approaches exist, such as single-root I/O virtualization (SR-IOV) and VirtIO. Articles in this section explore the I/O side of things. Containers and software VMs don't have to contend with these details as I/O is typically part of the software support provided to the isolated applications.
More Electronic Design TechXchanges
About the Author
William G. Wong
Senior Content Director - Electronic Design and Microwaves & RF
I am Editor of Electronic Design focusing on embedded, software, and systems. As Senior Content Director, I also manage Microwaves & RF and I work with a great team of editors to provide engineers, programmers, developers and technical managers with interesting and useful articles and videos on a regular basis. Check out our free newsletters to see the latest content.
You can send press releases for new products for possible coverage on the website. I am also interested in receiving contributed articles for publishing on our website. Use our template and send to me along with a signed release form.
Check out my blog, AltEmbedded on Electronic Design, as well as his latest articles on this site that are listed below.
You can visit my social media via these links:
- AltEmbedded on Electronic Design
- Bill Wong on Facebook
- @AltEmbedded on Twitter
- Bill Wong on LinkedIn
I earned a Bachelor of Electrical Engineering at the Georgia Institute of Technology and a Masters in Computer Science from Rutgers University. I still do a bit of programming using everything from C and C++ to Rust and Ada/SPARK. I do a bit of PHP programming for Drupal websites. I have posted a few Drupal modules.
I still get a hand on software and electronic hardware. Some of this can be found on our Kit Close-Up video series. You can also see me on many of our TechXchange Talk videos. I am interested in a range of projects from robotics to artificial intelligence.
Voice Your Opinion!
To join the conversation, and become an exclusive member of Electronic Design, create an account today!

Leaders relevant to this article: