11 Myths About Platform Security (.PDF Download)
The complexities of computer systems with tens of thousands of individual components, and even more lines of code, introduce many opportunities for oversights in proper system security. Each computer system may be interconnected with several other devices to form a network, and suddenly there are many points that can leave a system susceptible to misuse.
Below are 11 myths to be aware of when securing an embedded system.
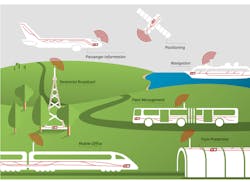
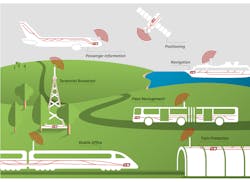
Growing use of connected systems has made data security even more of a focal point in embedded systems.
1. When buying a product, such as a hypervisor, the software takes care of all additional security concerns in virtualization.
The hypervisor is a software product that virtualizes hardware so that multiple operating systems (OSs) can be run independently on the same hardware. Part of the responsibility of the hypervisor is to isolate specific Oss; therefore, a breach in one doesn’t necessarily provide access to another.
However, a hypervisor will depend on several hardware features to help ensure that one virtual machine can’t interfere with another. For example, the memory management unit (MMU) will ensure the isolation of specific memory resources that have been assigned to each virtual machine. Also, the hypervisor provides a lot of flexibility, which means that a secure configuration of the virtual environment is necessary to ensure platform security.
2. Security is only a concern for the OS/hypervisor/application.
Each layer of the OSI model needs to be understood and secured. The whole boot process is vulnerable to infiltration in a system. To ensure that the complete boot process is secure, new features have become available. These include Intel TXT - Trusted boot in conjunction with TPM to ensure the boot process is secure and, if there are any changes, the system can be prevented from booting until there’s assurance of a secure boot environment.